People don’t usually fight about “everything.” They fight about what happened. Where someone was, what was said, who started it, or whether an excuse makes sense. When two stories clash, the loudest voice can start to sound like the “truth,” even when it isn’t.
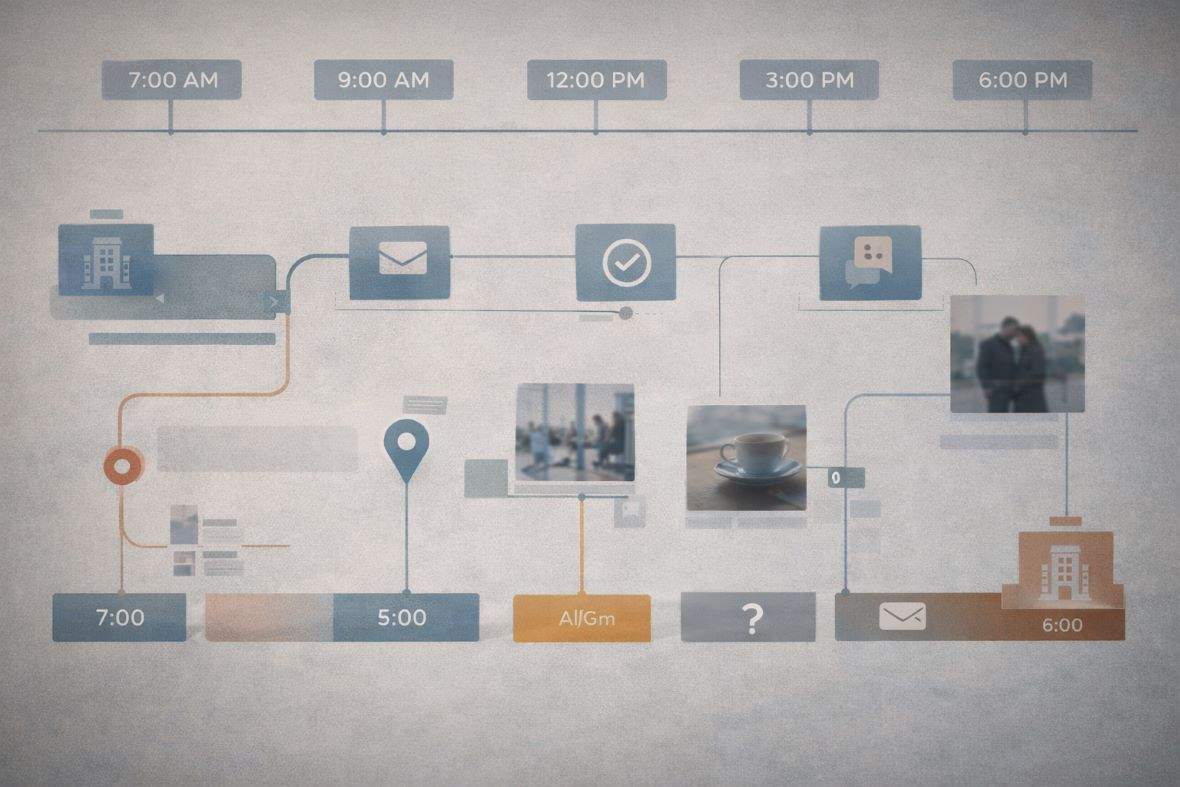
A viewpoint from a Private Investigator in Australia, many fact disputes become clearer once you build a legal timeline from digital footprints. A digital footprint is the trail a person leaves through everyday tech, like public posts, photo timestamps, app receipts a client already has, and device logs shared with consent. This isn’t hacking, and it isn’t about spying for sport. It’s about verifying reality with checkable details.
This article is general information, not legal advice. Evidence rules and privacy laws vary by state and situation.
Common reality disputes that a Private Investigator can help untangle with digital footprints

Fact disputes often feel personal, because they are. Still, the patterns repeat across relationships, family law, and day-to-day conflict. One person insists they’re being honest. The other feels gaslit. Meanwhile, the real issue is that no one can prove the timeline.
Digital footprints can help because they are often time-stamped and hard to “reinterpret” once verified. That said, one data point rarely settles anything. The job is to corroborate.
“You were there” vs “I wasn’t”, using location clues to test alibis
Location disputes show up everywhere, from breakup arguments to parenting conflicts. A client might say, “They told me they were at work,” but something feels off. Another client might be accused of being somewhere they swear they avoided.
A Private Investigator may test an alibi using lawful sources such as:
- A public social post tagged at a venue, even if it’s “just a quick selfie.”
- Timestamped photos, including the order they were taken and any visible landmarks.
- Ride-share or taxi receipts can be accessed in the client’s own email or app history.
- Public fitness activity maps (Strava-style), when the user’s profile is set to public.
- Real-world observations that match online activity, like a subject posting from a location while being seen arriving there.
The key is overlap. A check-in alone can be staged. A photo alone can be old. However, several independent clues can support or challenge a story.
The strongest timelines aren’t built on a single “gotcha.” They’re built from repeatable, cross-checked markers.
“That never happened” vs “It did”, using messages, timestamps, and patterns
Another common dispute is whether a conversation happened and what was actually agreed upon. This comes up in co-parenting, separation, and even everyday money disputes.
Digital footprints can help clarify this, especially when the client can provide the original material. Common examples include message timestamps, email threads, and patterns in call logs (shared with consent). Even email headers from client-provided emails can help confirm when a message was sent and how it moved through systems.
Screenshots are where many people get burned. They’re easy to crop, edit, or fake. Because of that, investigators look for supporting evidence, such as matching timestamps across devices, consistent contact details, and whether the same thread appears in more than one place. If someone claims “I never received it,” a delivery receipt or a follow-up reply may matter more than the screenshot itself.
Courts and tribunals often treat electronic material like any other document: it may need to be shown as relevant and authentic, not just persuasive. That’s why investigators try to work from original files and their metadata (the behind-the-scenes information that can help explain when something was created, how it was stored, and whether it appears consistent), rather than relying solely on screenshots. Digital-evidence best-practice guidance also stresses preserving the original data where possible, keeping an audit trail of what was done and when, and maintaining a clear chain of custody so the material can be independently reviewed if the matter becomes formal.
A practical, court-aware process for resolving fact disputes with digital evidence (without crossing legal lines)
Digital evidence can calm a dispute, or inflame it, depending on how it’s gathered and presented. A court-aware approach keeps the focus on observable facts and lawful methods. It also reduces the risk that evidence will be dismissed later.
At a high level, the process looks simple: define the claim, collect lawfully, verify carefully, then document clearly. The difference between helpful evidence and useless noise is how disciplined you are at each step.
Start with the claim, then map the “proof points” needed
When people are stressed, they argue in generalities. “You always lie.” “You’re imagining things.” A Private Investigator has to turn that heat into testable questions.
A practical way to do that is to write the claim as a single sentence, then break it into who, what, when, and where. For example:
- Who was present, and who can be independently identified?
- What action is being claimed, and what would it look like if true?
- When did it happen, and what time markers exist?
- Where did it happen, and what public traces might align with that place?
This step matters in relationships, too. When couples can’t agree on basic facts, they often get stuck in a loop where no repair happens. Daniel Dashnaw describes this dynamic in “Reality Disputes Create Communication Gridlock,” where partners fight over “reality” rather than solving the real problem. Clear proof points don’t “win” the relationship, but they can stop the endless replay.
Collect legally, verify carefully, and write it up so it holds up

Lawful collection is the foundation. In Australia, that generally means sticking to public information, using material the client owns or controls, and getting clear consent for any review of a device or account. It also means no hacking, no impersonation, and no secret tracking or recording that breaks state surveillance device laws.
In other words, “I can get into their accounts” is not a skill; it’s a red flag.
Verification is where good work lives. A careful investigator will:
- Preserve originals where possible, rather than relying on copies.
- Record source details, such as the URL, the visible timestamp, and the method of access.
- Note the date and time of collection, plus any relevant context.
- Store files securely, so they don’t get altered by accident.
This is also where the chain of custody comes in. If evidence ends up in a legal setting, you want to show it wasn’t tampered with and you can explain its origin. A clean report focuses on what was observed and what was provided, not speculation about motives.
Digital checks often work best when paired with real-world corroboration, such as surveillance footage from public places or witness-style documentation. That combination is common in relationship matters, including cases that later require an infidelity investigator’s services to document patterns in a court-friendly way.
Conclusion
Fact disputes don’t just waste time; they wear people down. Digital footprints can settle those disputes when a Private Investigator legally collects them, carefully verifies them, and cross-checks them against multiple sources. The goal isn’t to “catch” someone for the sake of it. It’s to restore clarity and fairness, especially when emotions are running hot.
If you’re in the middle of a reality battle, start by documenting what you already have: dates, receipts, original messages, and their sources. When the stakes are serious, seek licensed help so you don’t turn a search for truth into a legal problem.
Questions people ask before using digital footprints in an investigation
Digital evidence sounds straightforward until you’re the one living it. These are the questions that come up most, especially in relationship disputes.
Can a Private Investigator access someone’s private messages or email accounts?
No. A licensed Private Investigator shouldn’t hack, guess passwords, or access private accounts without authorisation. What can be used instead is public content, material the client already has lawful access to, or device and account information shared with clear consent. In some cases, formal legal pathways may apply, but that’s separate from “PI magic.”
Will digital evidence actually help in family law or a dispute with a partner?
Sometimes, yes, if it’s relevant, lawful, and tied to a clear timeline. Context still matters. A late-night message might be harmless, or it might support a broader pattern. The goal is to reduce guessing, not fuel more conflict. Strong reports stick to observable facts, because opinions are easy to attack.
How long does it take to verify a digital footprint claim?
It can take a few days for a narrow issue, or a few weeks if the data volume is large. Timing also depends on access, consent, and the need for corroboration. Rushing invites mistakes. When the stakes are high, investigators may combine digital checks with surveillance or interviews, when appropriate.
If you need help across state lines, it also helps to work with a team conducting a private investigation in Sydney, so the timeline doesn’t break when travel is required.
References
New South Wales. (2000). *Electronic Transactions Act 2000* (NSW). NSW Legislation. https://legislation.nsw.gov.au/view/whole/html/inforce/current/act-2000-008
New South Wales. (2007). *Surveillance Devices Act 2007* (NSW). NSW Legislation. https://legislation.nsw.gov.au/view/whole/html/inforce/current/act-2007-064
NSW Government. (2025, February 4). *Legal admissibility of digital records*. Retrieved February 23, 2026, from https://www.nsw.gov.au/nsw-government/recordkeeping/sentence-and-dispose/legal-admissibility-of-digital-records











